Whether your reasons are privacy-, compliance- or just curiosity-related, the good news is that self-hosting a captcha service is possible. Slightly worse news is that you will have to make a choice between sometimes mutually exclusive options, but we’ll talk about that later. And yes, you are reading a captcha comparison on a blog of the captcha provider itself, but I hope to surprise you.
Cap.js
Cap is a lightweight Proof-of-Work captcha service that you can freely (Apache 2.0 license at the moment) use in any kind of services. It is developed by a student from Lisbon, Portugal (according to their GitHub profile). It is primarily and foremost self-hosting-oriented product, without any kind of paid offering or licenses.
| Feature | Description | Comments |
|---|---|---|
| Stack | JavaScript + Redis | no comments |
| Producer | Tiago | no comments |
| Deployment | 5 out of 5 | Good docs, lean on resources, works out of the box |
| Protection | 2 out of 5 | PoW challenge difficulty does not scale dynamically (which is kind of the whole point of PoW) |
| Integrations | 1 out of 5 | Created just for JS frontend world, no other integrations available (including server-side) |
| Limits | no limits | Apache 2.0 license means commercial use is allowed out of the box |
Deployment / Stack
Technologically Cap consists of a stateless service implemented in JavaScript and a Redis Valkey in-memory store. On the bright side, this is certainly the leanest setup in this list and it offers solid features (below), but on the dark side, having no persistence layer (even though Redis Valkey can technically be persisted, it’s not designed for that) loses all historical data and useful insights. There’re no notions of accounts, reports or any other extra features besides the captcha itself.
Their self-hosting documentation is clear and accessible, oriented for Docker-based setup. It requires just 2 (yes, two!) environment variables: Redis URL and Admin secret. There isn’t much going on there. If you trust in JavaScript ecosystem, it’s a captcha that is the simplest to set up and get running. And it can probably run even on your Raspberry Pi.
Bot protection
In terms of bot protection, on top of “usual” Proof-of-Work, it adds instrumentation challenges, where there’s an obfuscated JS code that manipulates the DOM tree, but the author comments on it’s effectiveness:
Instrumentation is not foolproof. … I do not recommend using them as a replacement for proof-of-work. Without PoW and with a real browsers, attackers can cheaply mine these challenges.
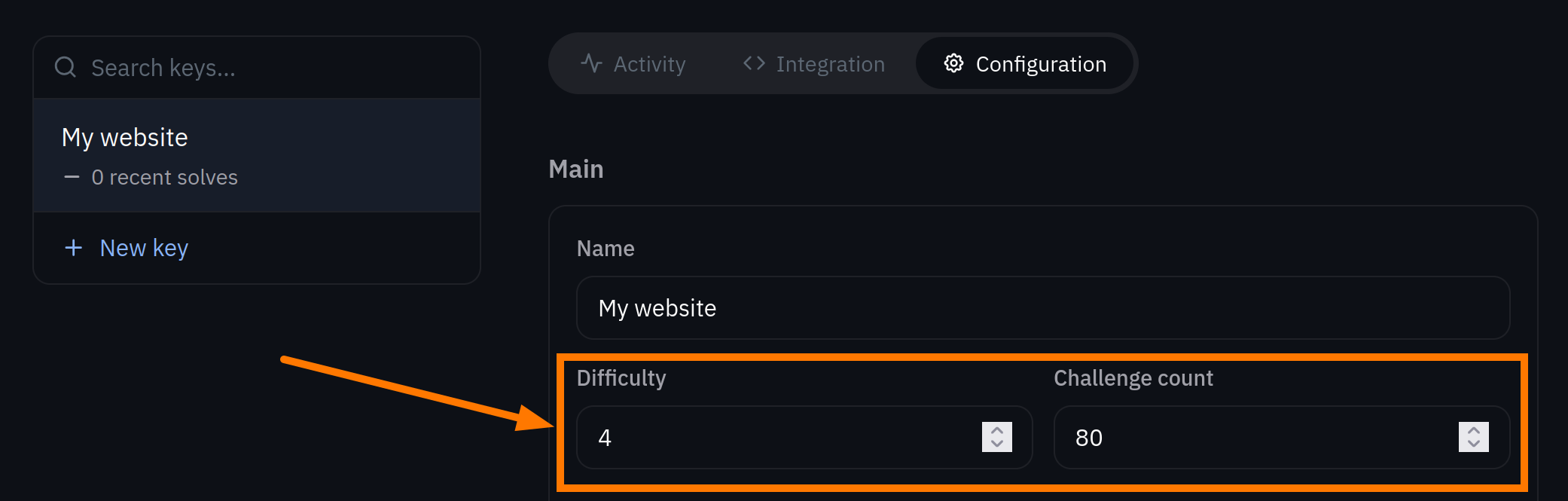
However, the major problem is that the challenges that it issues are not dynamic. The system does not adapt to variable bot activity and just always returns a single difficulty that you will configure in the dashboard.
This stacks on top of the fact that Cap.js does not have any kind of persistent storage for historical data (which is usually used to adjust the difficulty dynamically) which makes this issue somewhat worse.
Integrations
On a client-side (on your website) it is mainly designed to be used as a JavaScript component for modern JavaScript frameworks: React, Vue, Svelte, Astro, Preact and Qwik. There are no integrations for other technologies. For the server-side, a couple of quick snippets for verification are provided, but that is it.
Recommendations
Cap is really a great small tool if you need to deploy some captcha service fast. It’s modern, does not have annoying cognitive puzzles (like images etc.), fairly customizable, and definitely lightweight (both on server-side and client-side). Probably it does not stand a chance to be used seriously, but it certainly can be the right tool for the right job! Also, having Apache 2.0 license, it is not restrictive at all to be used for any kind of commercial projects.
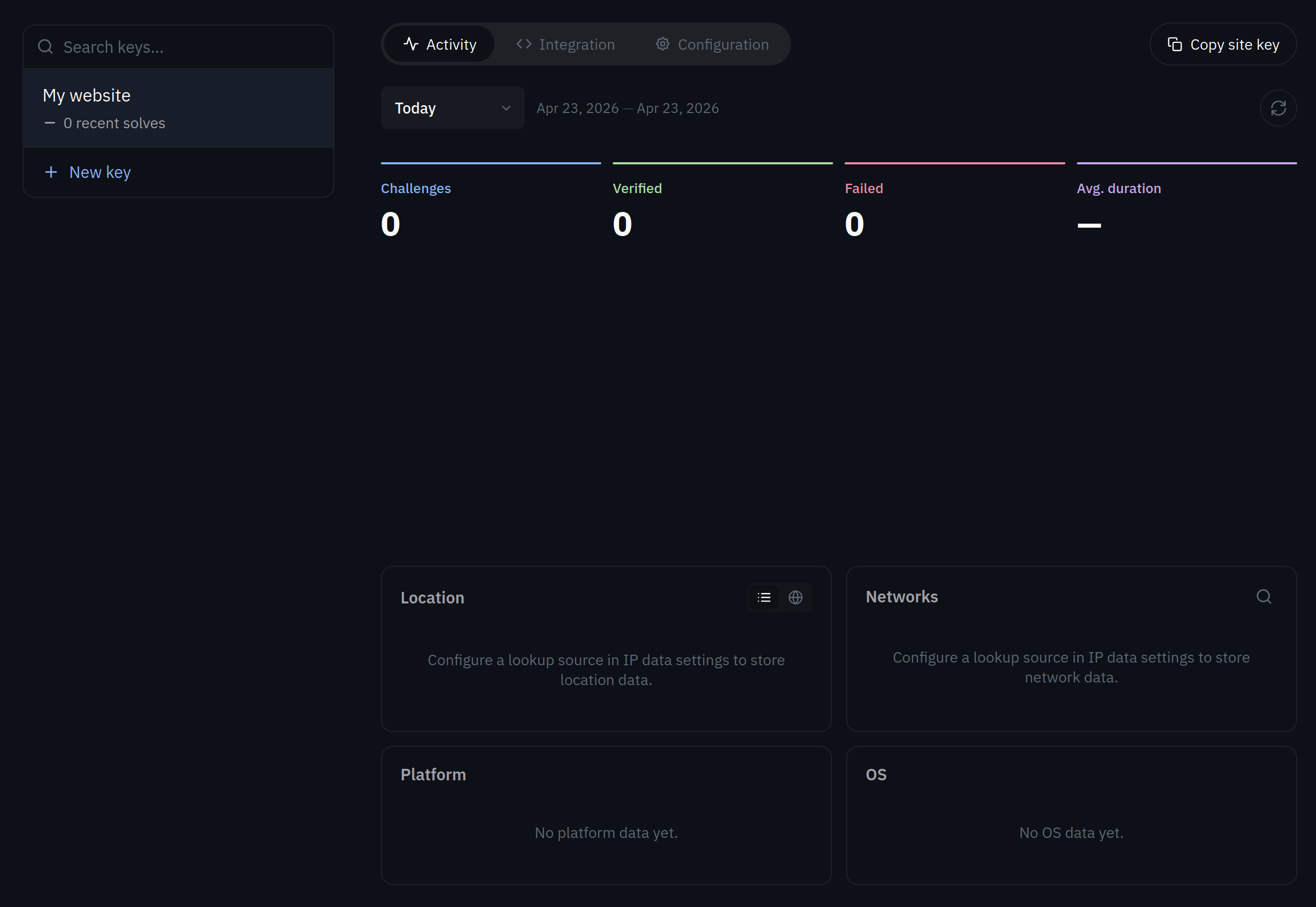
Altcha / Sentinel
OK, there’s an important distinction that has to be made: Altcha is mostly abandonware and the “actual Altcha” is the new proprietary closed-source Sentinel product that they are trying to sell. Of course, absolutely nothing is wrong with selling, but the confusion is real.
| Feature | Description | Comments |
|---|---|---|
| Stack | JavaScript + Postgres/Redis/ClickHouse | Kind of production-ready stack (sans the JS part) |
| Producer | BAU Software s.r.o. | Czeck republic, EU |
| Deployment | 3 out of 5 | Docs exist only for proprietary version, requires a lot of server resources to operate. Docker image is a 1 GB beast with questionable security (see below). |
| Protection | 5 out of 5 | Adaptive PoW captcha with few bells and whistles on top of that. |
| Integrations | 4 out of 5 | Solid amount of integrations both client- and server-side, likely covers 90% + of use-cases. |
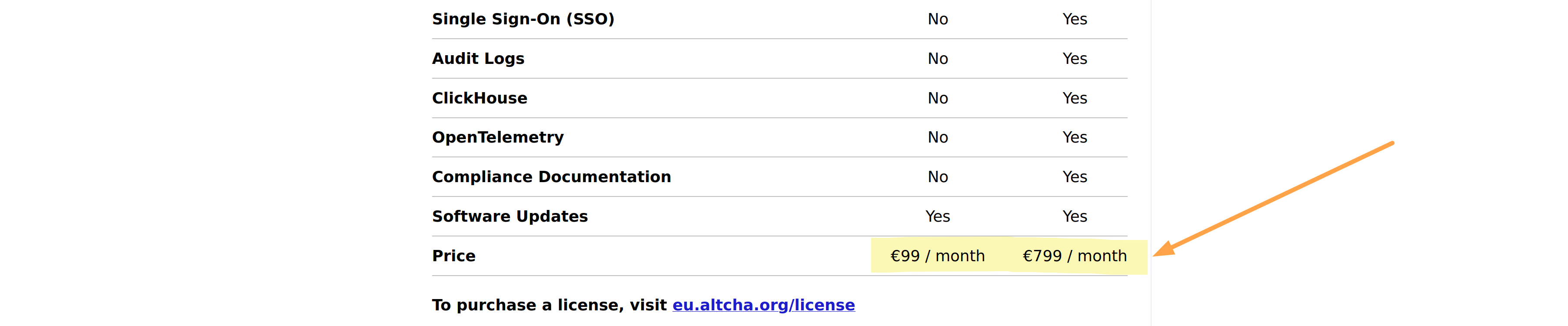
| Limits | Requires a license | License costs €99 / month or €799 / month. MIT-licensed version looks like abandonware. |
Deployment / Stack
Altcha
Neither Altcha repo on GitHub, nor their documentation mentions anything about how to self-host Altcha. Really. You’re on your own to figure out how (or if) to launch the beast.
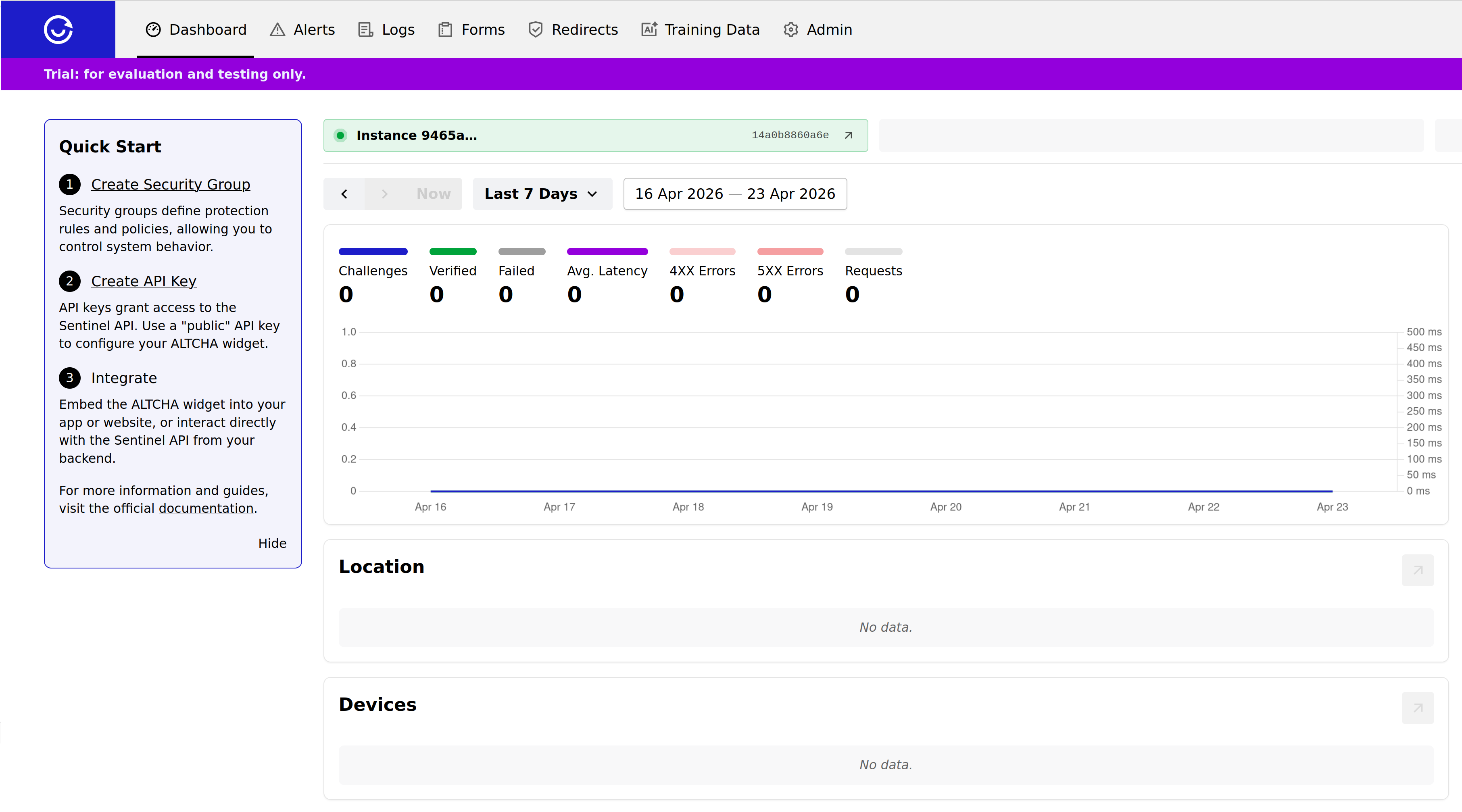
Sentinel
As for Sentinel, they do have the
self-hosting documentation that covers a number of installation methods: Docker, Kubernetes, AWS ECS, Azure or even Bunny with magical containers. But just that you know - you have 30 day free trial, then €99 or €799 per month.
Their Docker image (archived) is 450 MB and unarchived (running) it’s approx. 1.1 GB image beast. It is built on Debian bookworm to which their “server” layer 954 MB is added (you can explore it with the command dive ghcr.io/altcha-org/sentinel:1.26.0 if you have dive installed).
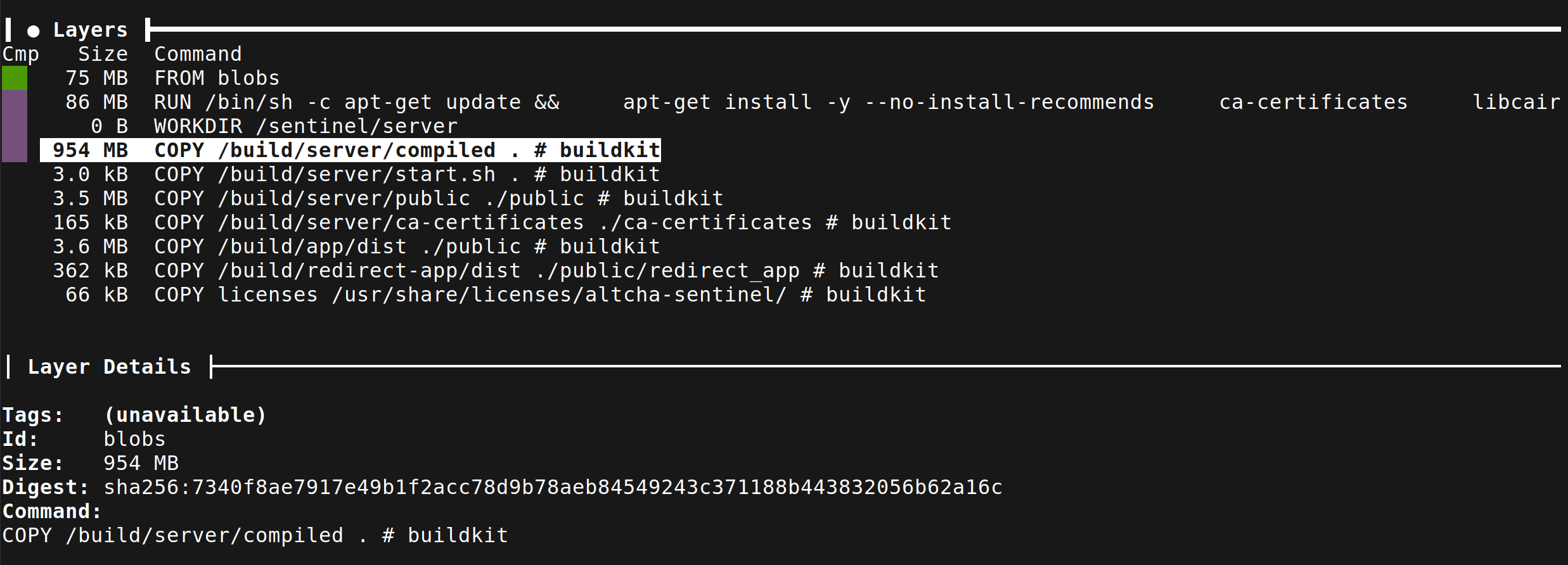
They ship everything: Python, Perl, all coreutils, terminal and even part of Docker itself (very “meta”). This is a security nightmare to deploy on premises, but let’s examine why their image is 1GB:
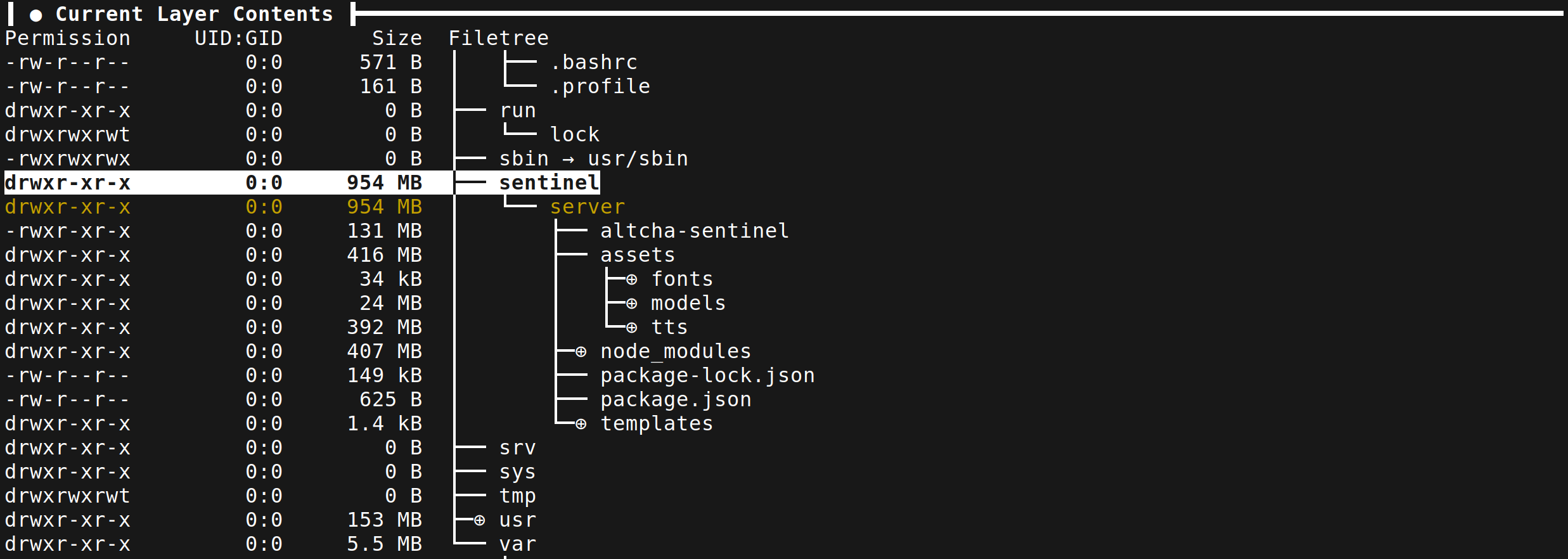
Even after we skip the mandatory joke about node_modules/ dir size of 407 MB, the server itself is 131 MB. Another 392 MB is taken by text-to-speech models with PCM files for different languages. Probably all for the “accessibility” to announce captcha text, like Google reCAPTCHA does when you give up to select fire hydrants?
In any case, this huge image is without any databases so you shall add that on top. To its credit, Altcha does support usual suspects like Redis, ClickHouse, Postgres as well as their managed variants from Azure or AWS. They also provide you with an “install” script that you are supposed to run on a freshly provisioned server: it installs docker and basic set of supporting coreutils and starts Altcha Sentinel from the docker-compose stack. You can check your options for the configuration
on this page.
Bot protection
Altcha offers adaptive Proof-of-Work, which is definitely a step-up from Cap.js. On top of that you do have more options if you opt to track your users: they have variants of the widget with recording user interactions, which they can optionally enrich with additional metadata (e.g. IP address score). All good and standard here.
They do offer a number of other features too, not strictly related to CAPTCHA:
- forms provider (you can use them kind of like Typeform or Tally, but stripped down to extreme essentials, yet with built-in captcha!)
- spam detection (email, website comments etc. - it works with Bring-Your-Own API keys from providers like OpenAI/Anthropic)
- links and redirects (you can proxy your page through Sentinel page, just like Turnstile does, but security usability here is kind of questionable)
Overall, their offering is very rich, at least on paper.
Integrations
Altcha offers a decent set of integrations, both on the client side and on the server-side. There are the usual suspects you would expect (even some more exotic ones too like Dart and C++). Most probably, you will be covered.
Recommendations
Altcha Sentinel is a full-featured captcha protection for sure, with on-prem/self-hosted setup available for multiple deployment options. It does have somewhat questionable security practices, but let’s leave it at that. However, it comes at a high monetary cost (and that is before the infra cost, which has higher requirements than other contenders in this list).
Private Captcha
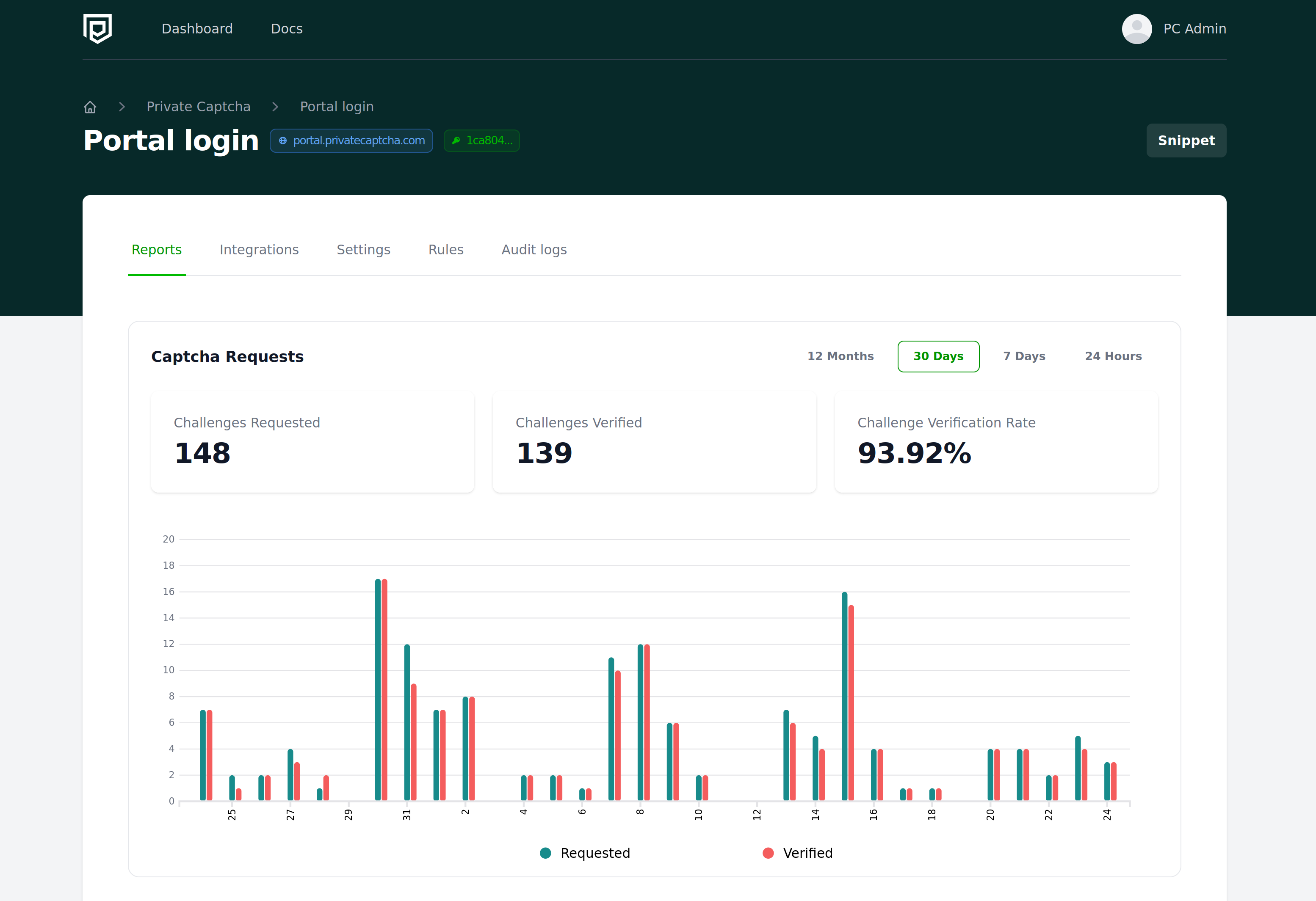
Private Captcha is a production-ready stack of captcha protection that was built for self-hosting/on-prem from the ground up. It’s absolutely free for non-commercial uses, and has licenses available for commercial ones. Private Captcha has SaaS offering (on this website privatecaptcha.com) that is funding its further development so the destiny of mCaptcha and others does not happen here.
| Feature | Description | Comments |
|---|---|---|
| Stack | Go + Postgres + ClickHouse | Production-ready stack |
| Producer | Intmaker OÜ | Estonia, EU |
| Deployment | 4 out of 5 | Docker-based stack is only available; Kubernetes setup is possible. |
| Protection | 5 out of 5 | PoW captcha with adaptive difficulty and extra features on top. |
| Integrations | 4 out of 5 | Solid amount of integrations, both client- and server-side, more in progress. |
| Limits | Free for non-commercial | Commercial licenses start at €11 / month |
Deployment / Stack
Private Captcha consists of Go server monolith that serves API, Portal and CDN; Postgres for business data (accounts, protection configuration etc.) and ClickHouse for historical analytics data that helps to select challenge difficulty based on patterns. Everything is self-contained (thanks to Go) and the server with everything is only about 40 MB. The only larger part of the stack is the ClickHouse itself, but it takes care of storing and querying a large amount of time series data efficiently. Private Captcha has an experimental mode running for completely without ClickHouse, but it might not be the best in terms of CAPTCHA challenge security if you plan to use it over a substantial time (kind of the weakness of Cap.js).
This is reflected in the deployment docs which provide a ready-made docker-compose.yml file. Overall deployment (with Docker) is rather simple, but keeping it running in production also requires setting up security correctly. None of the other projects ever mentions security setup in the docs, but it is one of the most important aspects.
Bot protection
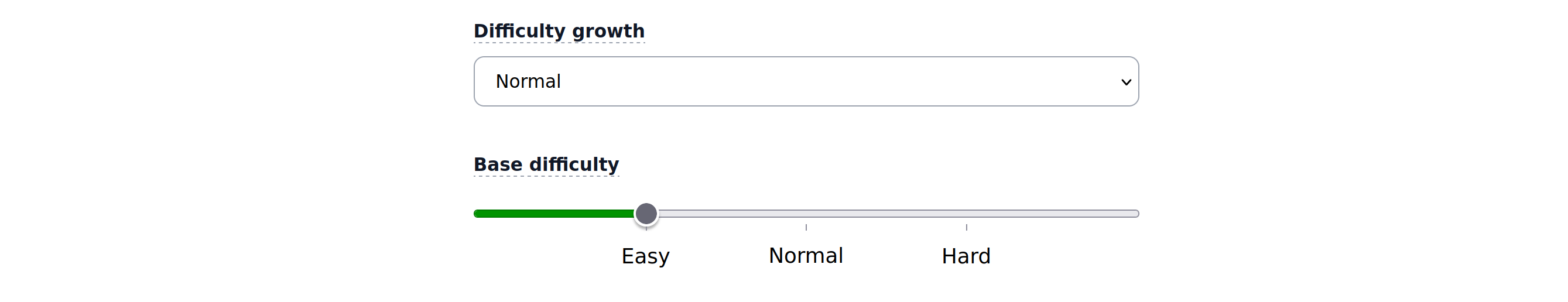
Private Captcha offers automatic difficulty scaling for proof-of-work challenges out of the box. In settings, you can configure “base” difficulty (minimum difficulty) and how reactive the growth is to traffic changes.
Also you have WAF-style difficulty rules that allow to additionally tune this difficulty, based on: User Agent, IP Address (e.g. Cloud providers, VPN, Tor, Firehol and others), Country, HTTP header value.
Integrations
Private Captcha has integrations on client- and server-side done for major platforms (e.g. WordPress) and technology stacks. All usual suspects are here.
Recommendations
you are reading this on privatecaptcha.com, we love Private Captcha here
Private Captcha has the focus on privacy and security (both deployment and of protected resources) and that power is available for self-hosting too. With more integrations being developed, it will soon be one of the most versatile options out there.
Others
Prosopo
Prosopo is a WordPress-oriented captcha and it’s one of those “fake self-hosted” products out there. This is the comment from the Prosopo founder on how to run self-hosted version:
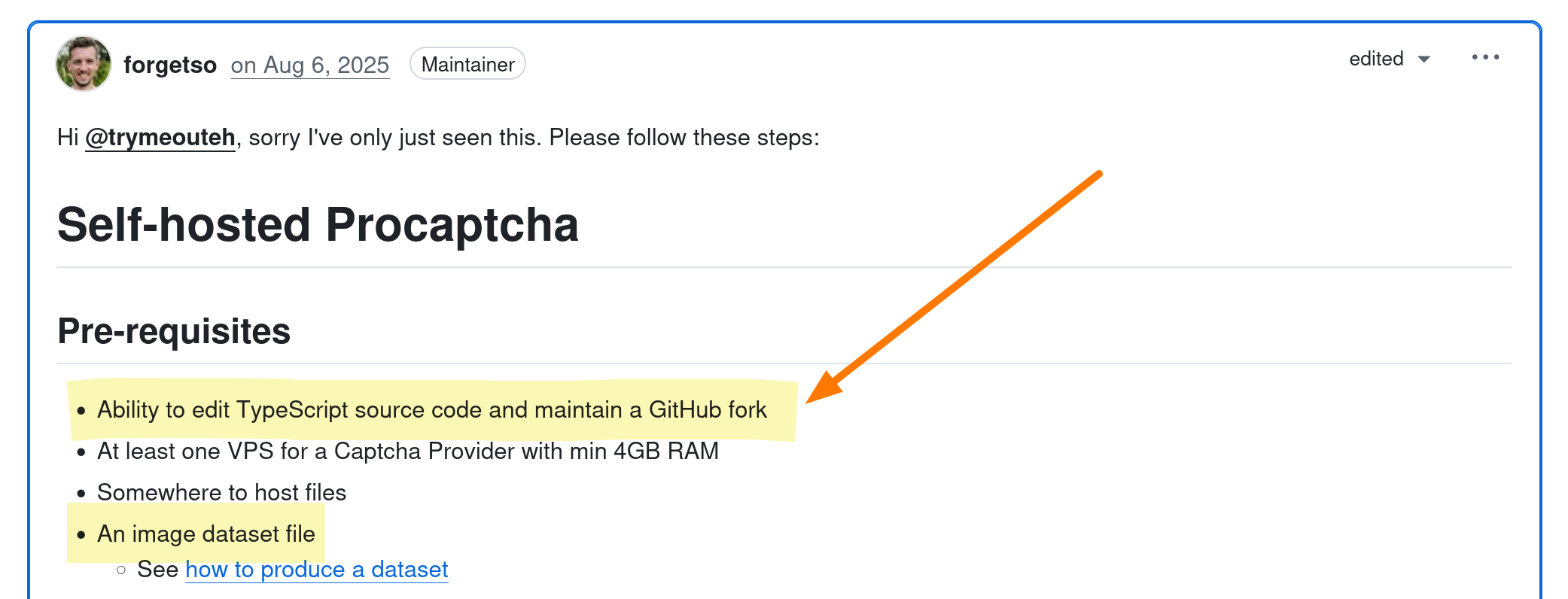
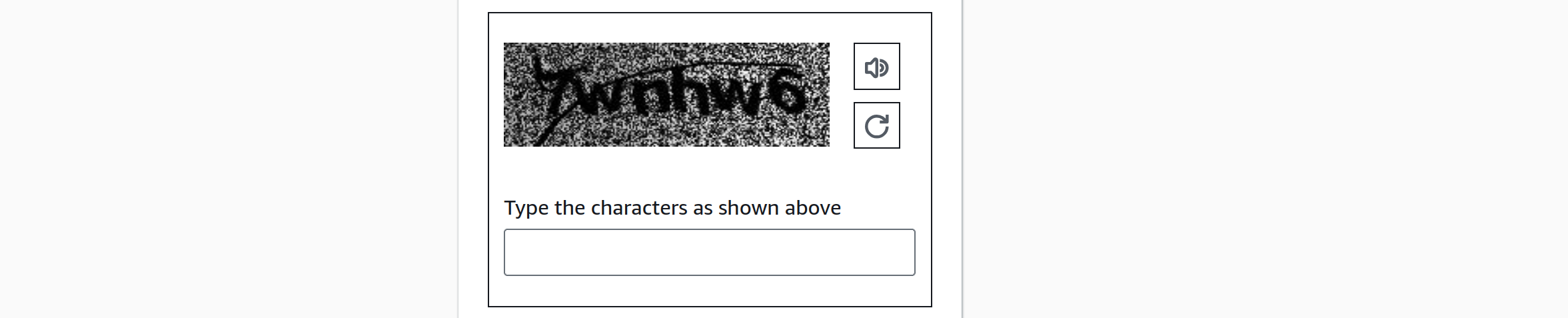
So to do self-hosting (per those instructions), you need to fork their GitHub repository, edit some Typescript files, generate your own dataset of images (remember CAPTCHAs from 2000s with skewed images? - the ones that Amazon is still using on AWS login screen in 2026):
Well, I can say this is more of a joke about self-hosted captcha service than the real deal. There are absolutely no sane instructions anywhere in the repo, client-side part of the widget for bot detection is proprietary and closed-source and the whole thing exists only so they can claim to be an “open-source captcha”.
Anubis / Wicketkeeper
Strictly, speaking, Anubis is not a CAPTCHA, but a proxy, that you deploy in front of your webservice (and Wicketkeeper being the less featureful version of Anubis). Its primary goal is protection against scraping and rate limiting of the website rather than form protection from bots, but one can argue it can help with it. Anubis is a great piece of software with a permissive license (replacing that anime logo requires a paid license, though) and very powerful configuration language. Not being captcha, it almost surely shouldn’t be in this list (for example, you cannot protect your login form with it, nor does it have any “integrations”), but it’s very close in a technological sense (proof-of-work protection) so I thought it belongs to this list.
mCaptcha
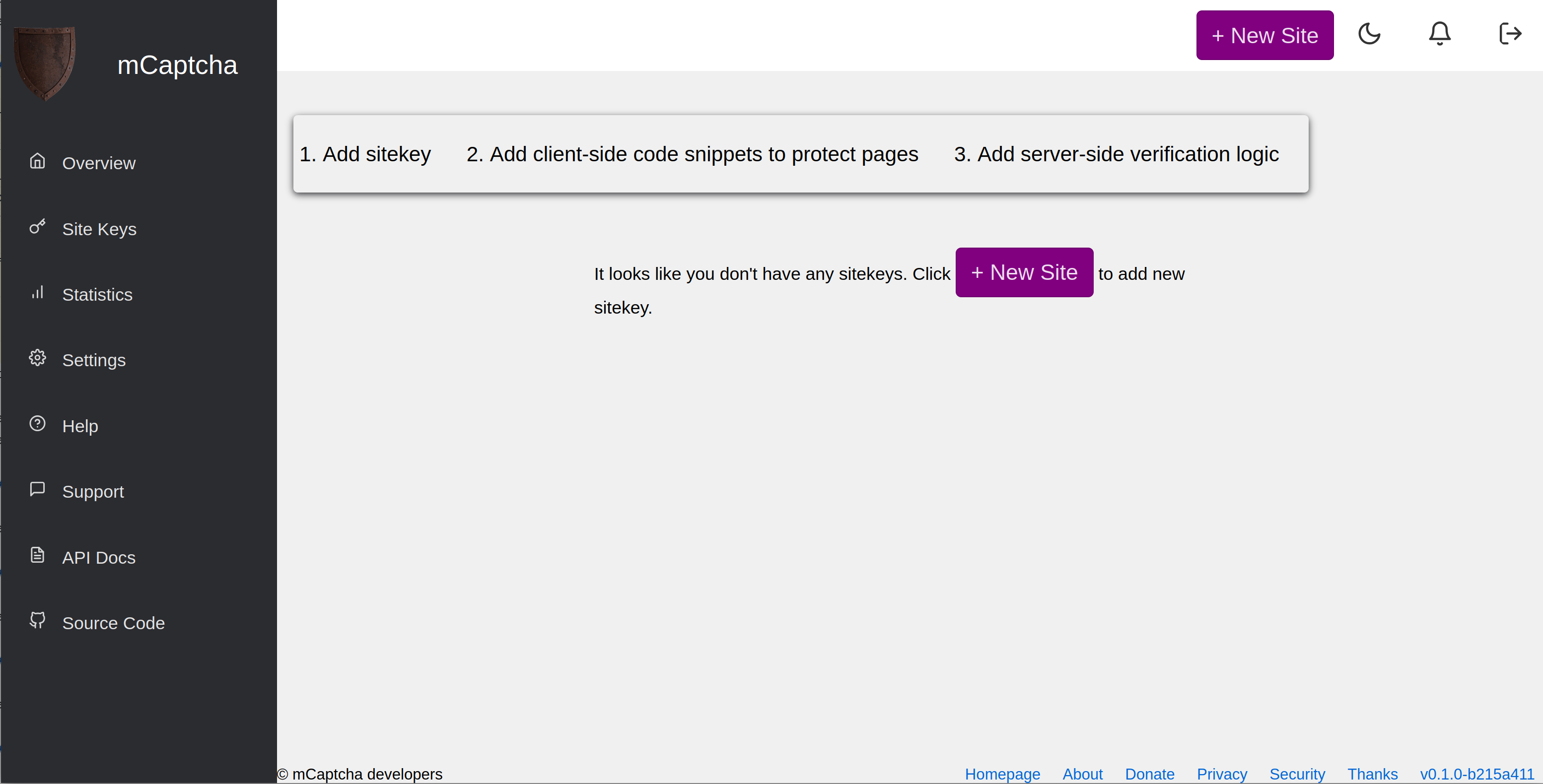
mCaptcha is one of the first self-hosted efforts to rewrite captcha in Rust have PoW self-hosted captcha, but it looks like an actual abandonware at this stage. It does work, though, but it looks and feels, let’s say, a bit rough over the edges. Its documentation is Okay and there are clear instructions on GitHub how to get started with the project and everything. It’s based on Postgres and Redis with Rust backend and JS frontend. But it just looks so unfinished that it’s just a bit hard to take seriously.

